Most proactive cybersecurity tools for SMEs are designed to stop attacks before damage occurs. That sounds sufficient. It isn’t.
In practice, most attacks don’t succeed before defenses activate or after alerts are triggered. They succeed during a narrow window where users are actively interacting with malicious environments and unknowingly handing over valid credentials. This is where most security stacks lose visibility. For SMEs, it is where most account takeovers (ATO) actually happen.
What “Proactive Cybersecurity” Actually Means for SMEs
Proactive cybersecurity is the strategic practice of stopping threats before they result in account takeover fraud or data loss . This requires a shift from reactive recovery to real-time intervention during the specific moment an attacker attempts to capture or reuse credentials.
In practice, this includes:
-
Preventing credential theft at the point of interaction.
-
Blocking unauthorized access before authentication is finalized.
-
Detecting suspicious activity as it occurs, rather than post-compromise.
However, most tools labeled “proactive” do not operate at the same stage of an attack. They either reduce risk before the attack begins or respond after suspicious activity is detected. For SMEs, this creates a practical problem: smaller teams, limited tooling, and a low tolerance for delayed response. The real question is not how many tools are deployed, but where they operate in the attack lifecycle.
The 6 Essential Categories of Proactive Cybersecurity Tools
Most SME security stacks combine a set of foundational categories to build a defensive perimeter. These typically include:
-
Endpoint protection platforms (EPP/EDR) for device-level threat blocking.
-
Identity and credential security tools for access management.
-
Network and DNS security tools for traffic filtering.
-
Vulnerability and risk management tools for system hardening.
-
Managed detection and response (MDR) for outsourced monitoring.
-
Security awareness and training platforms for human risk reduction.
While these tools are essential for overall hygiene, none fully covers the moment of attack execution. This leaves a critical blind spot at the exact moment credentials are entered.
So what actually matters when choosing a solution that can close this gap? To do that, you need to focus on capabilities that detect and disrupt attacks while they’re actively happening.
We’ve broken down these requirements in our guide on what actually matters when choosing an ATO solution, so you can evaluate your current stack against real-time threats.
Where Each Category Falls Short in Practice
| Category | What it protects | When it operates | Where it fails |
| Endpoint Protection | Devices and malware | Before/During execution |
No visibility into phishing sessions |
| Identity Security | Credentials and access | Before authentication |
Cannot stop real-time credential theft |
| Network & DNS | Traffic and connections | Before connection |
Weak against new phishing domains |
| Vulnerability Mgmt | Systems and code | Before exploitation |
Does not address user-targeted attacks |
| MDR | Systems and alerts | After detection |
Response delay leaves attacker window |
| Security Training | User behavior | Before attack |
Cannot eliminate human error |
The Execution Gap: Where Cybersecurity Tools Lose Visibility
The Execution Gap is the critical blind spot between initial prevention and final response where traditional security controls lose visibility. During this window, attackers succeed by influencing user behavior in real-time, often bypassing perimeters that were optimized for different stages of the lifecycle.
Because traditional tools focus on the “Before” (static risk) or the “After” (logged events), they are effectively blind while an attacker is actively harvesting or replaying credentials. One of the most common ways this happens is through cloned login environments that mirror your brand perfectly.
To understand the mechanics of this specific threat, it is vital to examine how website cloning detection & ATO strategy work together to expose the attacker’s presence before the session is finalized.
What is the Execution Gap?
The Execution Gap is the point where:
-
Users interact with attacker-controlled environments.
-
Credentials are captured or reused in real time.
-
Sessions appear legitimate to traditional monitoring.
-
Traditional controls lose visibility, allowing the attack to succeed.
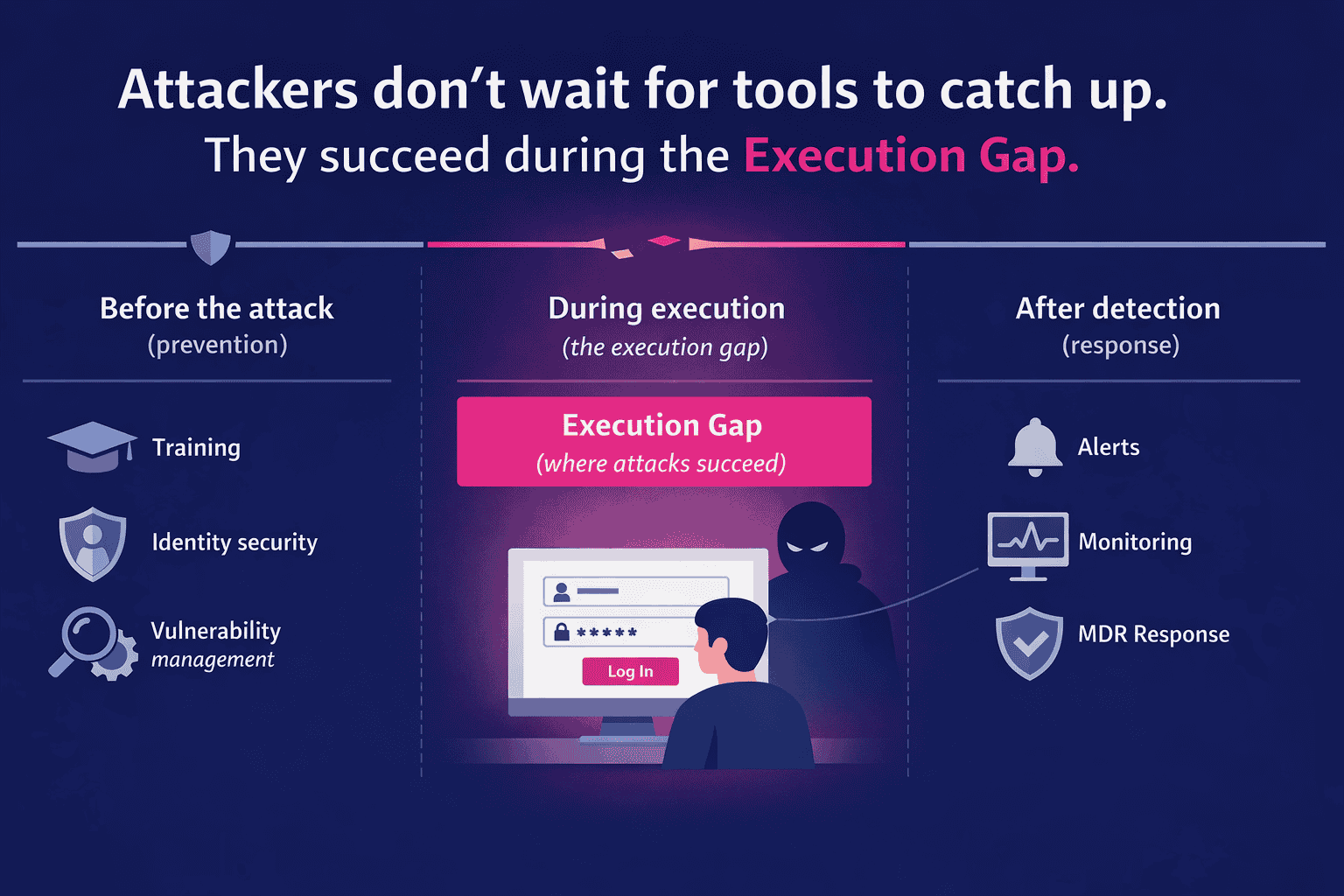
How the Gap Shows Up in Real Environments
-
Before the attack: Training and vulnerability scanning reduce exposure, but they do not stop a user from entering credentials into a convincing phishing flow.
-
At the perimeter: Endpoint and network controls block known threats but struggle with targeted or newly created digital impersonation infrastructure.
-
After detection: MDR and response workflows investigate suspicious activity, but often after valid credentials have already been used.
Modern attacks do not rely on malware; they rely on valid user behavior inside attacker-controlled flows. Because credentials are correct and sessions look legitimate, most security tools are no longer in a position to intervene.
Closing the Execution Gap: A Different Security Model
Closing the Execution Gap requires shifting protection from identifying threats to controlling outcomes during the attack itself. This means moving beyond static perimeters and focusing on the live interaction between the user and the malicious environment.
This shift toward earlier intervention isn’t just theoretical; independent analysts are now calling for a fundamental change in how enterprises defend their digital perimeters. You can read the full breakdown of What Frost & Sullivan says enterprises need to understand why traditional proactive tools are no longer sufficient in a landscape dominated by execution-stage threats. By aligning with this preemptive model, organizations can move from reactive remediation to real-time disruption.
What Changes When You Focus on Execution
Instead of relying on signals before or after the attack, protection shifts to live interaction monitoring:
-
Detecting when users interact with impersonation environments.
-
Identifying credential harvesting as it happens.
-
Recognizing sessions influenced by attacker-controlled flows.
-
Correlating session and device behavior across interactions.
-
Introducing decoy credentials to invalidate stolen data.
How This Differs from Traditional Controls
Traditional tools operate around the attack: endpoint tools block access, and identity tools strengthen credentials. Execution-stage protection operates inside the attack itself. It focuses on controlling outcomes when credentials are already in play.
For SMEs, this shift is practical because it reduces reliance on large security teams and removes dependency on perfect user behavior.
How to Evaluate Your Current Security Stack
Building an effective stack requires aligning tools to the full attack lifecycle, ensuring there are no unmonitored windows between prevention and response. Use the following diagnostic to identify where your current visibility stops:
-
Map your tools to the attack lifecycle: Categorize each tool as Before, During, or After execution.
-
Identify the visibility cutoff: Determine if you can see credential capture and session manipulation as they happen in the browser.
-
Test your exposure: Simulate a user entering credentials into a cloned environment to see if any alerts trigger before the “Log In” button is pressed.
Can your current team identify a breach before the session is finalized? Shifting the primary security metric from post-incident containment to real-time prevention requires visibility into the “During” phase of the attack. You can see how this model allows you to Detect Account Takeover Attempts in the First 5 Minutes by closing the window between credential exposure and unauthorized access. Prioritizing tools that operate during active credential use, rather than just around it, is the only way to effectively close the Execution Gap.
Close the Execution Gap Before It’s Exploited, With Memcyco
Most security stacks look complete on paper. But if they don’t operate during the moment credentials are captured or reused, they leave the most critical stage exposed.
The question is not whether you have proactive tools.
It’s whether you have visibility and control when an attack is actually unfolding.
Start by pressure-testing your current stack:
- Can you detect when a user interacts with a phishing or impersonation environment?
- Can you identify credential capture as it happens, not after?
- Can you act before those credentials are used to take over an account?
If the answer is unclear, that’s the gap.
Memcyco is designed to operate exactly where traditional controls lose visibility, during the execution phase, when credentials are in play and sessions still appear legitimate. It gives security and fraud teams the ability to detect, understand, and disrupt attacks before damage occurs.
Book a product tour to see how execution-stage protection works in real time, and what your current stack is missing.
FAQs
What are proactive cybersecurity tools? Proactive cybersecurity tools are solutions designed to prevent attacks by reducing exposure, blocking threats, and detecting suspicious activity before damage occurs.
Are endpoint protection tools enough for SMEs? No. Endpoint tools protect against malware but do not detect phishing-based credential theft that occurs outside the device.
How do phishing attacks bypass traditional tools? They rely on legitimate user interactions, allowing attackers to capture credentials without triggering malware or network-based alerts.
What is the biggest gap in proactive cybersecurity? The biggest gap is the Execution Gap, where credentials are stolen or reused in real time without visibility from traditional controls.

Julian Agudelo is Head of Content, a cybersecurity writer at heart, and his focus at Memcyco covers phishing attacks, digital impersonation, and account takeover fraud. His work translates complex threat intelligence into practical insights for security and fraud leaders. Julian focuses on the tactics used in modern impersonation campaigns and how organizations can better protect customers and digital channels from evolving online fraud threats.