Introduction
Most brand impersonation protection programs are built around a process that starts after the damage is done. A fake site goes live. Customers land on it. Credentials get stolen. Then the takedown request goes in. That sequence isn’t a workflow problem. It’s an architectural one.
Preemptive brand impersonation protection means intervening before credentials are entered, not after a cloned site is discovered. It requires real-time visibility into customer interactions with fraudulent assets, and the ability to disrupt an active attack while it’s still running.
This article examines why the takedown model is structurally insufficient, what genuine preemptive protection looks like in practice, and how security leaders can assess whether their current program is actually protecting customers or just documenting attacks after the fact.
The Gartner Mandate Has Arrived – and Brand Protection Teams Are Not Ready
In October 2025, Gartner formally named preemptive cybersecurity one of its Top Strategic Technology Trends for 2026. That’s not a forecast. It’s a capital allocation signal for the next three to five years.
Gartner frames preemptive cybersecurity around three core strategies: deny, deceive, and disrupt. The explicit goal is to neutralize threats before they cause damage. Gartner projects preemptive cybersecurity will account for 50% of IT security spending by 2030, up from less than 5% in 2024.
Now apply that definition to how most brand impersonation protection programs actually work today.
A threat intelligence feed flags a suspicious domain. An analyst reviews it. A takedown request goes to the registrar. The provider responds, eventually. The fake site comes down. The team logs the incident as resolved.
That loop isn’t preemptive by any measure. It doesn’t deny attackers access to victims, deceive them, or disrupt their operations while the attack is live. It cleans up infrastructure after it’s already been weaponized. The gap between the Gartner definition and the standard brand protection workflow isn’t a matter of degree. It’s categorical.
Here’s the kicker: most brand protection vendors know this. They’ve responded by making the reactive loop faster, with better crawlers, AI-assisted detection, and streamlined takedown workflows. These are real improvements. But they’re optimizations of a fundamentally post-hoc model. Faster remediation is still remediation.
Gartner isn’t asking security teams to run the same play more efficiently. It’s asking them to change the play entirely. Preemption means intervening before a customer enters a single credential on a fake site, not after the site has been live for 48 hours.
For brand impersonation protection, that requires a different architecture. Not a faster version of the same loop.
The Window of Exposure Is Not a Gap – It Is the Attack
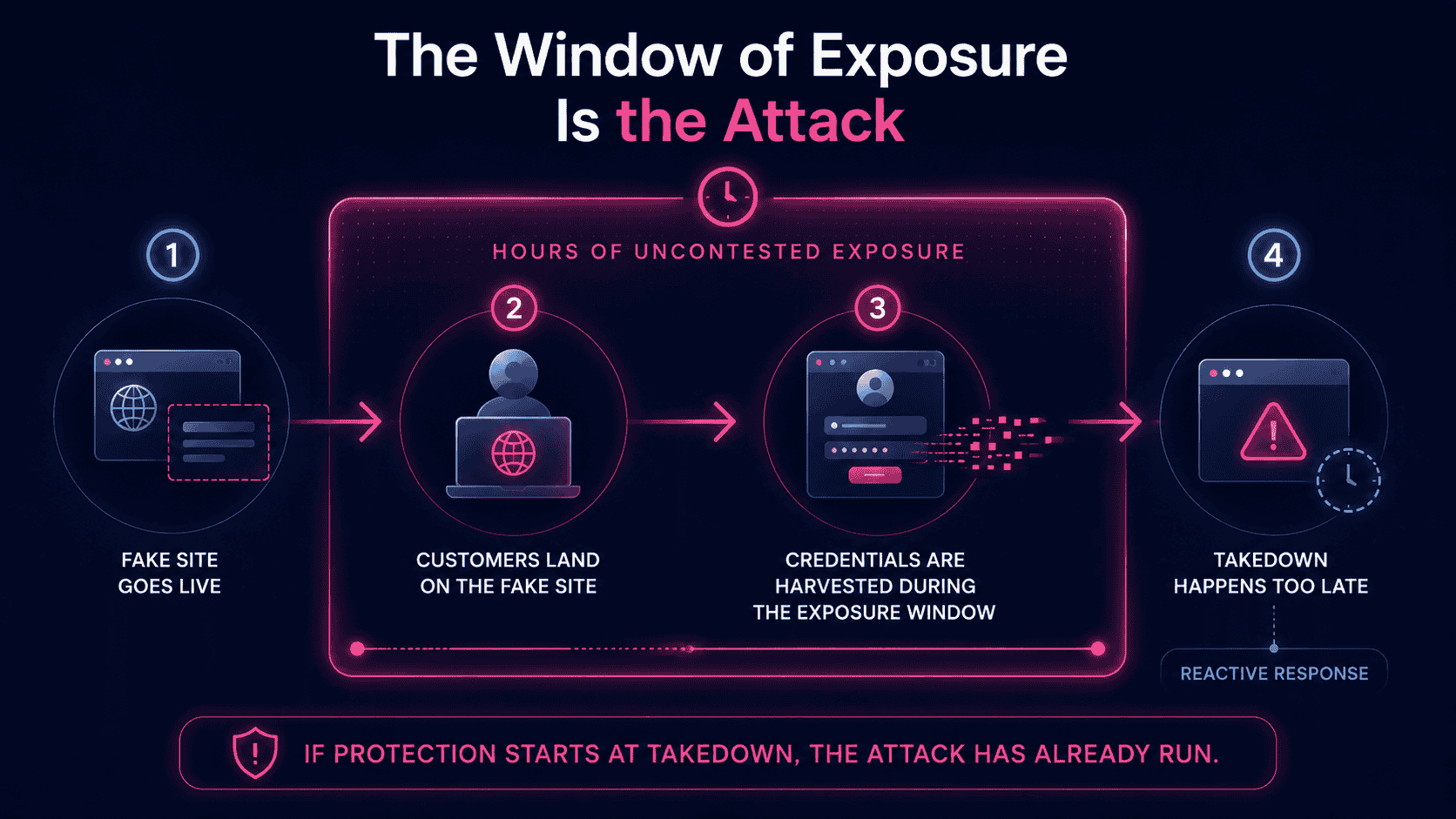
Here’s the uncomfortable truth about takedowns: by the time one succeeds, the attack is already over.
The window of exposure is the period between a fake or cloned site going live and its eventual removal. Most security teams treat it as a process inefficiency, something to tighten with better tooling or faster vendor SLAs. That framing is wrong. The window isn’t a gap in the process. It’s the attack itself.
Research published at the ACM Web Conference 2025 (Lim et al., “Seven Days Later: Analyzing Phishing-Site Lifespan After Detection”) found that phishing websites stay active for an average of 54 hours after detection, with a median of 5.46 hours. Google Safe Browsing is slow to register these sites, particularly those using redirection and evasion techniques, meaning many phishing operations terminate before blocklist-based defenses even flag them. Separately, SlashNext’s 2024 Phishing Intelligence Report recorded a 703% surge in credential phishing attacks in the second half of 2024 alone.
Think about what 54 hours of uncontested access actually means.
A cloned banking login page goes live on a Sunday evening. It ranks in search results, circulates via SMS, and runs through social media ads. By Monday morning, hundreds of customers have entered their credentials. By Tuesday, thousands have. The takedown request is filed. The site comes down Wednesday. The team marks the incident closed.
Not a single stolen credential was recovered. Every account compromised during those 54 hours remains at risk. The takedown didn’t undo the attack. It cleaned up the infrastructure after the attack had already concluded.
Now make the harder argument: even a one-hour takedown doesn’t solve this.
Every customer who visited the fake site during that hour was exposed. Their credentials were captured. Attackers spin up phishing and clone sites knowing they have hours of uncontested access. The short lifespan is a feature, not a flaw. Burn the site, spin up another, repeat.
Cutting the takedown window from 54 hours to 12 hours doesn’t change the structural reality: the model requires the attack to have already launched, and customers to already be at risk, before any protective action is possible.
Faster takedowns aren’t the answer. They’re a faster version of the wrong answer.
Why Legacy Brand Protection Tools Are Reactive by Design, Not Just by Speed
The problem with most brand impersonation protection tools isn’t that they’re slow. It’s that they’re built to be slow.
Every major brand monitoring and takedown service runs on the same fundamental loop: crawl the web, detect a fake site that already exists, report it to a registrar or hosting provider, and wait for removal. That sequence has a hard structural constraint baked into step one. Before any protective action is possible, the attack must have already launched. Adding AI to the detection layer makes step one faster. It doesn’t change what step one is.
That’s not preemption. That’s faster reaction.
The endpoint security industry learned this lesson the hard way. Traditional antivirus relied on signature-based detection: match a known threat pattern, block it. The model worked until attackers started writing novel malware that no signature database had ever seen. The response wasn’t to build a faster signature database. It was to change the architecture entirely. EDR platforms emerged in the early 2010s, shifting from “does this match a known bad thing?” to “is this behavior consistent with an attack in progress?” Cisco describes this as the move from prevention-focused platforms to detection and response, fundamentally changing the threat model.
Brand impersonation protection hasn’t made that shift.
The answer is partly historical. Brand protection grew out of trademark enforcement and domain monitoring, disciplines built around legal remediation rather than real-time technical intervention. Sending a takedown notice to a registrar is a legal act, not a security act. The tooling inherited that DNA.
The result is a category built around cleaning up infrastructure after it’s already been weaponized. BrandShield, ZeroFox, PhishLabs, Netcraft, and others have built sophisticated detection and takedown capabilities within that model. The issue isn’t their execution. The issue is the model itself.
You can’t make a post-hoc remediation workflow preemptive by accelerating it. The intervention point is wrong. And as long as the intervention point is wrong, the window of exposure stays open.
The Endpoint Security Parallel: A Lesson Brand Protection Has Not Learned
Cast your mind back to the early 2000s. Antivirus software worked on a simple premise: catalog every known threat, then scan for a match. If the signature wasn’t in the database, the threat walked straight through.
The industry hit a wall fast. Novel malware, zero-day exploits, and polymorphic code made signature matching structurally useless against anything new. The response wasn’t to build a faster signature database. It was to abandon the model entirely.
The shift to behavioral detection changed the question from “have we seen this threat before?” to “is something behaving like a threat right now?” That architectural pivot produced EDR, then XDR, then SIEM integration. As Forrester notes, XDR is explicitly defined as the evolution of EDR, unifying behavioral detections across endpoints, email, identity, and cloud. The category didn’t just get faster. It got fundamentally different.
Brand impersonation protection is sitting at the exact same inflection point, and hasn’t moved.
The takedown model is signature-based detection by another name. A fake site has to be found, catalogued, and reported before any protective action is possible. The attack has already launched. Customers are already on the page. The “signature,” the known phishing URL, only gets added to the blocklist after victims have been exposed.
The behavioral equivalent would monitor what customers are actually doing in real time: specifically, whether they’re interacting with a site impersonating a legitimate brand. Intervene at that moment, not after the fact.
The technology to do this exists. The architectural shift, at the category level, has not happened. That’s not a vendor problem. It’s a category-wide blind spot.
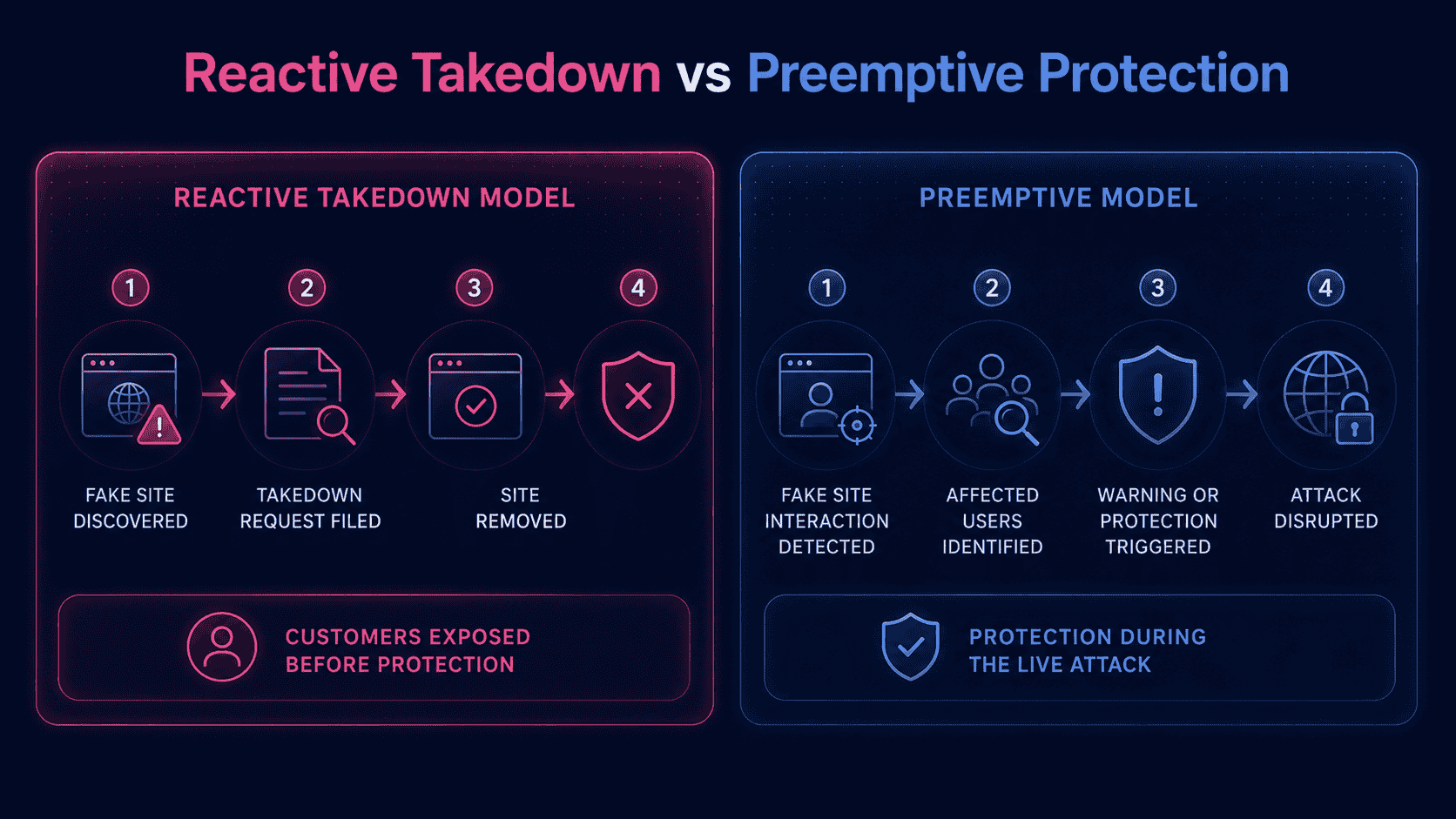
What Preemptive Brand Impersonation Protection Actually Looks Like
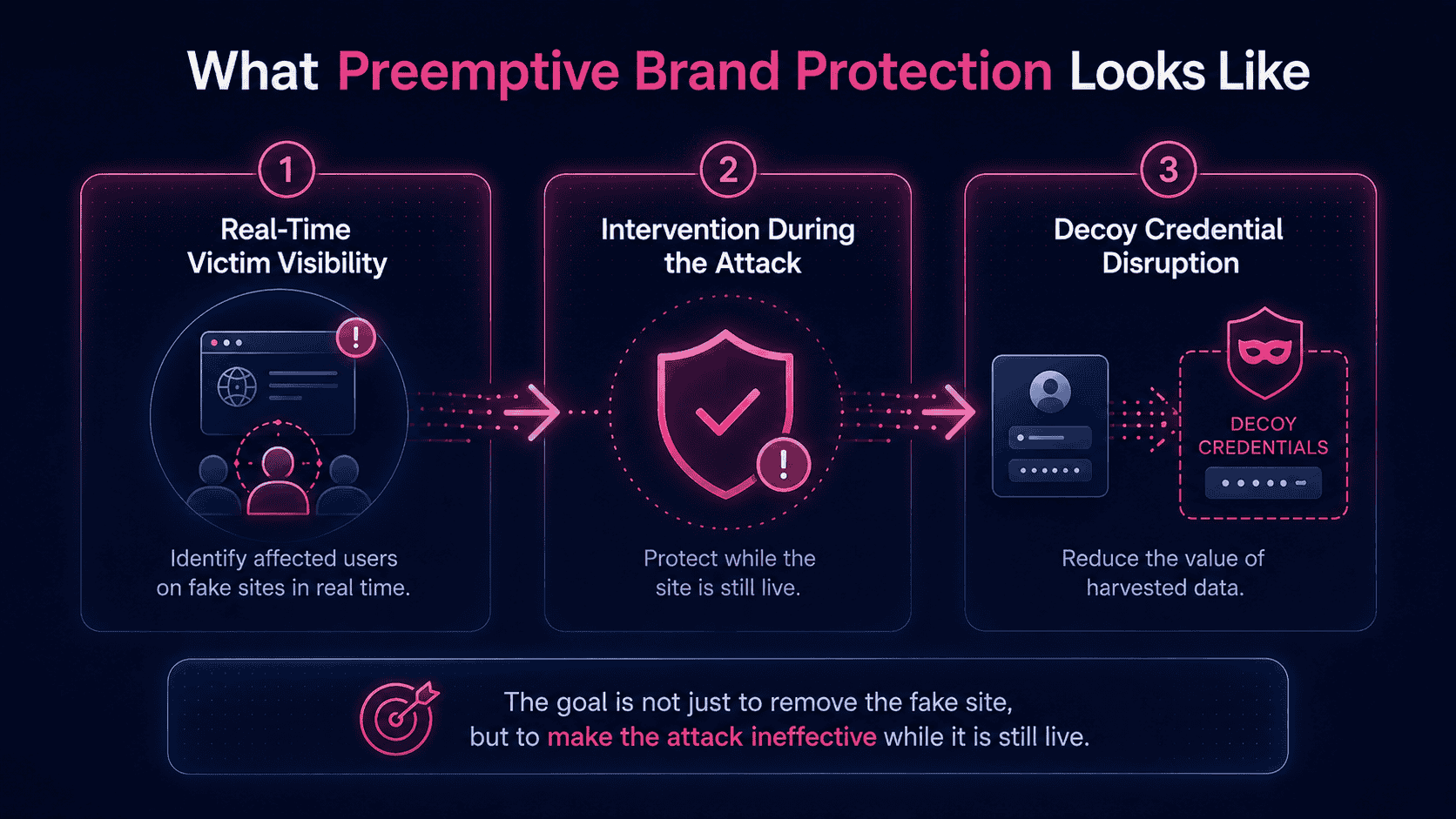
Faster takedowns aren’t the answer. A fake site that’s live for even one hour can harvest hundreds of credentials. Research published in 2025 found that the average phishing site lifespan is 54 hours, with a median of just 5.46 hours, meaning a significant share of attacks are designed to burn fast and disappear before any takedown request clears. A genuinely preemptive model requires something structurally different across three operational dimensions.
- Dimension one: real-time victim visibility
Most brand monitoring tools tell you a fake site exists. That’s not the same as knowing a customer is on it right now.
Preemptive protection requires more than external crawlers scanning the web for suspicious domains. When a customer interacts with an impersonation asset, security teams need real-time visibility into the exposure event, the affected user, and the associated risk context. The visibility layer has to connect impersonation exposure to user and access signals while the attack is still active, not after the site has already been reported.
- Dimension two: intervention during the attack
Knowing a customer is on a fake site is only useful if you can act while they’re still there.
Consider two scenarios. In the first, a customer clicks a phishing link and lands on a cloned bank login page. Before they type a single character, they receive a real-time warning that the site is not authentic. They leave. The attacker harvests nothing. In the second, the customer doesn’t see the warning and submits their credentials. A preemptive system intercepts the form submission and replaces the real credentials with decoy data. The attacker receives false information. The real credentials are never compromised.
In both cases, the fake site is still live. The takedown hasn’t happened. But the attack has already failed.
- Dimension three: attacker deception and intelligence
Decoy credentials do more than protect individual victims. They degrade the entire attack.
When attackers consistently receive false data, the harvested credential list becomes worthless. On top of that, the decoy data generates intelligence: attacker behavior patterns, infrastructure signals, and session data that security teams can act on. Your dashboard stops showing a retrospective report of who was exposed last week. It shows a live feed of an active attack in progress, with individual victim identification and session-level detail.
This is the key distinction between preemptive and reactive brand impersonation protection. The goal isn’t to remove the fake site faster. It’s to make the fake site ineffective while it’s still live. The site can stay up for days. If no real credentials are harvested and every victim is warned or protected, the attack has failed, regardless of when the takedown finally arrives.
The Downstream Consequences Security Leaders Are Accountable For
The window of exposure isn’t just a security metric. It’s a direct line to your fraud P&L.
Credential theft from brand impersonation attacks is one of the primary feeders for account takeover fraud. Stolen logins harvested from a fake site at 9am are draining accounts by noon. The scale is unforgiving: ATO losses are projected to reach $17 billion in 2025, up from $13 billion the prior year, per Sift’s Q3 2025 Digital Trust Index. ATO incidents surged 250% in 2024, per Kasada’s 2025 Account Takeover Attack Trends Report. The FBI reported over $262 million in ATO-related losses in the first ten months of 2025 alone, tied specifically to impersonation of financial institutions.
The reactive model doesn’t just fail to stop these losses. It actively enables them by leaving the credential harvesting window open.
Then there’s the trust dimension, which security teams consistently underweight in board conversations. Customers who get victimized on a fake site don’t blame the attacker. They blame the brand. According to Menlo Security’s State of Browser Security Report, nearly 51% of browser-based phishing attacks involve brand impersonation. 75% of consumers will cut ties with a brand after a cyber incident, and most blame the company for failing to protect them.
Churn, inbound support volume, and NPS erosion are real, measurable costs that never appear in the incident report.
The financial math is equally brutal. The IBM Cost of a Data Breach Report 2025 puts the average breach cost in financial services at $5.56 million. That’s the average. Where credential theft feeds downstream fraud at scale, the exposure compounds fast.
The reactive model doesn’t just leave a gap in your defenses. It transfers the full cost of the attack onto your brand and your customers.
How Memcyco Operationalizes the Preemptive Model
The preemptive model isn’t a roadmap item. It’s a deployed capability with documented outcomes.
Memcyco’s architecture is built to identify impersonation exposure while attacks are still active, not after fake infrastructure has been removed. Instead of relying only on external discovery and takedown, Memcyco connects signals from impersonation activity, affected users, devices, and subsequent access attempts, giving teams real-time visibility into attacks as they unfold.
The key difference is the detection point. Traditional brand protection starts with fake-site discovery. Memcyco adds visibility into real user exposure, helping teams identify when customers are interacting with impersonation assets and respond while the attack is still live.
That architectural difference produces three capabilities no takedown service can replicate.
- Real-time victim identification. The security team sees exactly which customers are on the fake site right now, with session-level detail. Not a retrospective report filed after the attack concluded. A live feed of an active attack, as it happens.
- Active disruption. When a customer submits a form on the fake site, Memcyco substitutes their real credentials for decoy credentials. The attacker receives false data. The actual credentials are never harvested.
- Attacker deception. By feeding false signals into the attacker’s infrastructure, Memcyco degrades the campaign’s value and generates intelligence about attacker behavior, tooling, and infrastructure.
Deployment is agentless. No end-user installation required. Customers don’t need to download anything, change their behavior, or even know the protection exists. Protection scales to the entire customer base immediately upon deployment.
The outcomes are documented. Customers report up to a 50% reduction in ATO incidents and up to 90% reduction in investigation time, with 10x ROI within the first year. One CISO at a top-10 North American bank stated: “They took our incident handling times from 72 hours to less than one hour and saved us millions every month.”
External validation reinforces this. Frost & Sullivan’s 2025 Global Transformational Innovation Leadership Recognition in the fraud detection and prevention industry concluded that “Memcyco has launched a preemptive solution to detect and stop fraud before it occurs.” David Mattei, Strategic Advisor at Datos Insights, observed that “Memcyco’s technology provides financial institutions with visibility into fraud attempts before credentials are compromised, addressing a persistent blind spot in traditional security frameworks.”
The preemptive model is running in production at financial institutions today, closing the window of exposure the takedown model structurally cannot.
A Maturity Framework for Evaluating Your Current Brand Impersonation Posture
Here’s the uncomfortable question most security leaders haven’t formally asked: is your brand impersonation protection program built to meet the Gartner preemptive cybersecurity standard, or is it built around the model that standard was designed to replace?
Four diagnostic questions will tell you.
- Question 1: Does your solution detect attacks before or after customers are exposed?
If detection depends on crawling the web for fake sites, the answer is after. The fake site must exist, be indexed, and be discoverable before any alert fires. A preemptive model detects the attack at the moment of customer contact, regardless of whether the fake site has been catalogued. Menlo Security’s State of Browser Security Report found the average window of exposure before legacy tools begin blocking zero-hour phishing pages is six days. Six days of uncontested customer access. If your detection model requires the site to be found first, you’re already behind.
- Question 2: Can you identify individual victims in real time during a live attack?
Most brand monitoring platforms can confirm a fake site exists. Very few can tell you which specific customers are on it right now, with session-level detail. Knowing a specific customer is currently on a fake login page lets you act before they submit a single credential. Aggregate traffic estimates don’t give you that. Real-time victim identification does.
- Question 3: Does your response capability intervene during the attack or after it concludes?
Takedown is a post-attack response. It removes infrastructure after the attack has already executed. Preemptive intervention, whether that’s warning a customer, substituting decoy credentials, or disrupting attacker workflows, happens while the attack is still live. If your only response lever is a takedown request, your program concludes after the damage is done.
- Question 4: What is your average window of exposure, and how many customers are exposed during that window?
If you can’t answer this with real data, your tooling isn’t giving you the visibility to assess your actual risk. If your answer is measured in hours or days, the structural math of the takedown model is working against you.
If these questions reveal a reactive posture, the issue isn’t your vendor’s execution speed. It’s the architectural model your program is built on.
Gartner projects that preemptive cybersecurity will account for 50% of IT security spending by 2030, up from less than 5% in 2024. That shift is already underway. The question is whether your brand impersonation protection program is architected to move with it.
The Architecture of Protection Has to Match the Speed of the Threat
Attackers don’t wait for your takedown request to expire.
AI has compressed the attack timeline to a point where the old model isn’t just slow. It’s structurally irrelevant. Cofense’s 2026 Annual Report found that malicious phishing emails are now deployed every 19 seconds, more than double the pace of 2024. Fake sites spin up in minutes. Credentials are harvested in hours. Stolen logins are monetized before most security teams have filed a takedown.
The Gartner preemptive cybersecurity mandate isn’t a forecast about where threats are heading. It’s a recognition of where they already are.
Security and fraud leaders who still evaluate brand impersonation protection on takedown speed are optimizing the wrong variable entirely. The question isn’t how fast you can remove a fake site. It’s how many of your customers were harmed before it came down.
If your answer is “we don’t know” or “some, but we filed quickly,” that’s not a preemptive program. It’s a reactive one with good reporting.
The technology to identify individual victims on a fake site in real time, disrupt the attack while it’s live, and close the window of exposure before a single credential is entered exists today. The outcomes are measurable. The architectural shift is real, but it isn’t theoretical.
As AI continues to lower the cost and complexity of spinning up convincing fake sites, that window of exposure will only compress further. The brands that close it before credentials are stolen will retain customer trust. The ones that keep waiting for the takedown will keep paying for the damage it leaves behind.
Conclusion
Phishing sites harvest credentials in hours. Takedowns take days. That gap isn’t a process failure you can optimize away. It’s a structural mismatch between the speed of the threat and the architecture of most brand impersonation protection programs. Closing it requires intervening during the attack, not after it concludes.
Is Your Brand Impersonation Protection Actually Preemptive?
See how Memcyco platform identifies customers on fake sites in real time and disrupts attacks before credentials are entered – no takedown required.
FAQs
Q: What is the difference between brand impersonation protection and anti-phishing software?
A: Anti-phishing software typically focuses on filtering malicious emails before they reach users, operating at the email gateway layer. Brand impersonation protection addresses a broader threat: fake websites, cloned login pages, and fraudulent digital assets that impersonate a brand to steal customer credentials – threats that exist entirely outside the email perimeter. The most important distinction is the intervention point: anti-phishing tools act before the user receives a message, while most brand impersonation tools act after a fake site is discovered. A preemptive brand impersonation solution like Memcyco intervenes at the moment a customer lands on a fake site – before credentials are entered – regardless of how they arrived there.
Q: How long does a phishing site typically stay live before it is taken down?
A: Research published in 2025 (Lim et al., WWW 2025) found that phishing websites remain active for an average of 54 hours – approximately 2.25 days – with a median of 5.46 hours. Critically, Google Safe Browsing takes an average of 4.5 days to detect these sites, meaning many phishing operations complete their credential harvesting and shut down before blocklist-based defenses even register them. This data underscores why the takedown model is structurally insufficient: the attack is often complete before the takedown is initiated.
Q: What does ‘preemptive cybersecurity’ mean in the context of brand protection?
A: Gartner formally identified preemptive cybersecurity as a top strategic technology trend for 2026, defining it around three core capabilities: deny, deceive, and disrupt – with the goal of neutralizing threats before they cause damage. Applied to brand protection, preemptive cybersecurity means intervening at the moment a customer lands on a fake site, before credentials are entered, rather than removing the fake site after the attack has already executed. It requires real-time visibility into customer interactions with impersonating assets, the ability to identify individual victims during a live attack, and active disruption capabilities – such as substituting real credentials for decoy data – that make the fake site ineffective while it is still live.
Q: How does account takeover fraud connect to brand impersonation attacks?
A: Brand impersonation attacks – fake websites, cloned login pages, phishing sites – are one of the primary credential harvesting mechanisms that feed account takeover (ATO) fraud. Attackers steal credentials from customers who believe they are logging into a legitimate brand’s site, then use those credentials hours or days later to access real accounts, initiate transfers, or commit identity fraud. ATO fraud losses are projected to reach $17 billion in 2025 (Sift Q3 2025 Digital Trust Index), and ATO incidents surged 250% in 2024 (Kasada 2025 Account Takeover Attack Trends Report). Closing the brand impersonation window of exposure is therefore a direct upstream intervention in the ATO fraud chain.
Q: Can a brand impersonation protection solution work without installing software on customer devices?
A: Yes. Agentless deployment is critical for protecting an entire customer base at scale. Memcyco requires no software installation, app download, or behavior change from end users. Instead, proprietary Nano Defenders help surface real-time signals from active impersonation attacks, allowing security teams to identify affected users and take protective action while the attack is still live. This enables broad customer protection without adding friction to the digital experience.
Q: What metrics should security leaders use to evaluate their brand impersonation protection program?
A: Four diagnostic metrics reveal whether a brand impersonation protection program is genuinely preemptive or structurally reactive: (1) Detection timing – does your solution detect attacks before or after customers are exposed? (2) Victim visibility – can you identify individual customers on a fake site in real time, or only after the fact? (3) Intervention timing – does your response capability act during the attack or after it concludes? (4) Window of exposure – what is your average time between a fake site going live and the moment your first customer is protected? If any of these metrics is measured in hours or days, the architectural model of your current program is working against you.